Welcome, builders! In the event you’ve frolicked mastering information constructions and algorithms, have you ever thought of their encrypted information potential?
Introducing the world of Totally Homomorphic Encryption (FHE), a groundbreaking strategy that enables for computations on encrypted information with out ever needing to decrypt it. This implies you may carry out operations on information whereas sustaining full privateness. This employs post-quantum cryptographic strategies, permitting encrypted information to stay safe on public networks reminiscent of clouds or blockchains.
On this sequence of articles, we discover how conventional information constructions and algorithms, like binary search timber, sorting algorithms, and even dynamic programming strategies, could be carried out in an encrypted area utilizing FHE. Think about performing a binary search on a dataset that is still completely encrypted, or sorting information that’s not seen in its uncooked kind, all whereas guaranteeing that the privateness and safety of the information are by no means compromised.
We’ll dive into how FHE works at a elementary stage and the implications it has for each information safety and algorithm design. Later on this sequence we’ll additionally discover real-world purposes and the potential challenges builders face when implementing these encrypted algorithms, reminiscent of fraud detection, funds, and extra. This isn’t nearly enhancing safety; it’s about rethinking how we work together with information and pushing the boundaries of what’s doable in software program improvement.
Whether or not you’re a seasoned developer or new to the idea of encrypted computing, this text will offer you insights into how one can combine superior cryptographic strategies into your programming tasks. Let’s embark on this journey collectively and unlock the potential of coding in cipher, remodeling on a regular basis information operations into safe, privacy-preserving computations that pave the way in which for a brand new period of safe digital innovation.
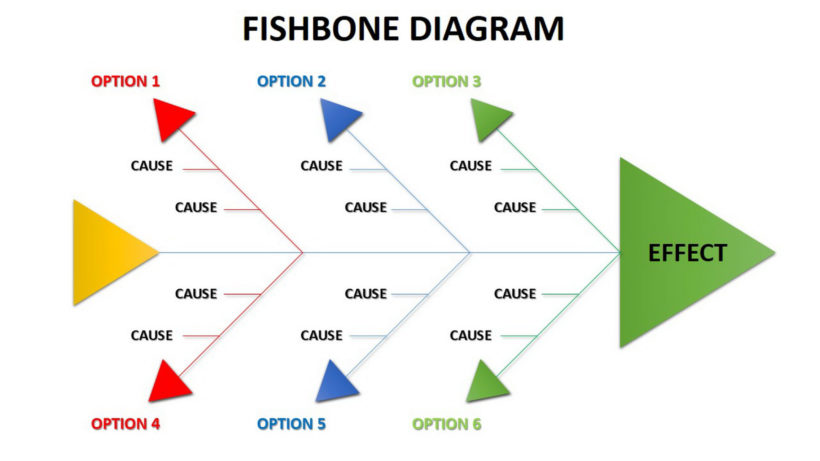
The 2 major sorts of operations that may be carried out on ciphertexts in FHE are addition and multiplication, although these function constructing blocks for extra complicated operations. As an example, you may add two encrypted values, and the outcome, when decrypted, would be the sum of the unique plaintext values. Advanced computations could be constructed utilizing combos of those primary operations, permitting for algorithms and capabilities to be executed on encrypted information. For instance, now we have a perform F that takes two enter values x and y and computes x + x * y. A mathematical illustration of this perform is written as F(x, y) = x + x * y, which will also be represented as a circuit, which is in different phrases, a direct acyclic graph:
Whereas FHE permits computations on encrypted information, it comes with the added problem of noise development inside ciphertexts, which may ultimately result in decryption errors if not correctly managed. In FHE schemes, each ciphertext consists of some quantity of noise that ensures safety. This noise is small initially however grows as extra operations are carried out on the ciphertext. When performing an addition operation, the noise is comparatively small, nonetheless, when multiplying, the noise from every of the 2 ciphertexts multiplies collectively within the product. This in flip ends in a a lot increased noise stage. Particularly, if you happen to multiply two ciphertexts with noise ranges n1 and n2, the noise within the ensuing ciphertext could be approximated as n1 * n2, or a perform rising a lot quicker than both n1 or n2 alone.
There are a couple of methods to mange the noise in FHE schemas, however for the sake of article size, the primary focus is on the noise discount method known as bootstrapping. Bootstrapping reduces the noise stage of a ciphertext, thus restoring the noise finances and permitting extra computations. Basically, bootstrapping applies the decryption and re-encryption algorithms homomorphically. This requires evaluating the complete decryption circuit of the FHE scheme as an encrypted perform. The output is a brand new ciphertext that represents the identical plaintext as earlier than however with diminished noise. Bootstrapping is a crucial method in FHE that enables for primarily limitless computations on encrypted information.
To make your very first steps in exploring FHE, you could delve into the premade circuits within the open supply IDE discovered at fhe-studio.com, which relies on the Concrete FHE library. Concrete’s FHE schema (a variation of the TFHE schema) is binary based mostly, so every bit is individually encrypted. The implementation robotically selects bits per integer utilizing the developer’s instance. Concrete additionally permits for computerized noise administration, vastly lowering complexity and growing accessibility for novice customers. Let’s look right into a easy circuit that provides 2 numbers:
from concrete import fhe#1. outline the circuit
def add(x, y):
return x + y
# 2. Compile the circuit
compiler = fhe.Compiler(add, {"x": "encrypted", "y": "clear"})
# examples to find out what number of bits to make use of for integers
inputset = [(2, 3), (0, 0), (1, 6), (7, 7), (7, 1)]
circuit = compiler.compile(inputset)
# 3. testing
x = 4
y = 4
# clear analysis (not encrypted)
clear_evaluation = add(x, y)
# encrypt information, run encrypted circuit, decrypt outcome
homomorphic_evaluation = circuit.encrypt_run_decrypt(x, y)
print(x, "+", y, "=", clear_evaluation, "=", homomorphic_evaluation)
The compiler then compiles the circuit right into a format known as MLIR, which is seen to the person after compilation is full:
module {
func.func @essential(%arg0: !FHE.eint<4>, %arg1: i5) -> !FHE.eint<4> {
%0 = "FHE.add_eint_int"(%arg0, %arg1) : (!FHE.eint<4>, i5) -> !FHE.eint<4>
return %0 : !FHE.eint<4>
}
}
As soon as the circuit is compiled, you may add it into your FHE Vault and you’ll share your circuit for others to carry out the identical encrypted computations.
The FHE schema used within the IDE natively helps the next operations:
1. Addition
2. Multiplication
3. Extract a bit (since each bit is encrypted individually)
4. Desk lookup
The primary three are fairly easy, nonetheless, the final one requires some consideration. Let’s have a look at the instance beneath:
desk = fhe.LookupTable([2, -1, 3, 0])@fhe.compiler({"x": "encrypted"})
def f(x):
return desk[x]
It acts as an everyday desk — if x=0, then f = 2 and similar for the remaining: f(1) = -1; f(2) = 3; f(3) = 0.
Desk Lookups are very versatile. All operations besides addition, subtraction, multiplication with non-encrypted values, tensor manipulation operations, and some operations constructed with primitive operations (e.g. matmul, conv) are transformed to Desk Lookups below the hood. They permit Concrete to help many operations, however they’re costly. The precise value is determined by many variables ({hardware} used, error chance, and so forth.), however they’re all the time far more costly in comparison with different operations. You need to attempt to keep away from them as a lot as doable. Whereas it’s not all the time doable to keep away from them utterly, it’s best to attempt to scale back the overall variety of desk lookups, as an alternative changing a few of them with different primitive operations.
The IF operator shouldn’t be native to FHE, and it must be utilized in an arithmetical method. Let’s have a look at the next instance:
if a > 0:
c = 4
else:
c = 5
In FHE, we should care for all of the branching as a result of it isn’t doable to instantly see the information, so the code turns into the sum of two expressions the place one is 0 , and the opposite is 1:
flag = a > 0 # yields 1 or 0
c = 4 * flag + 5 * (1 - flag)
Recall, that a > 0 shouldn’t be a local in FHE. The most straightforward implementation is to make use of a lookup desk . Let’s assume that the constructive variable a is 2 bit, then a> 0 for all of the (4) outcomes, besides when a equals 0. We are able to construct a desk for all of the outcomes of the 2 bits of a: {0,1,1,1} . Then the circuit will appear like this:
desk = fhe.LookupTable([0, 1, 1, 1])@fhe.compiler({"a": "encrypted"})
def f(a):
flag = desk[a] # a > 0, for 2bit a
return 4 * flag + 5 * (1 - flag)
It is very important word that, if a turns into bigger than 2 bits, the scale of the corresponding lookup desk grows very quick, leading to a rise in dimension of the evaluating key for the circuit. In Concrete FHE implementation this strategy is a default performance for the comparability operator. For instance, this circuit:
from concrete import fhe@fhe.compiler({"x": "encrypted"})
def less_then_21(x):
return x < 21
inputset = [1, 31]
circuit = less_then_21.compile(inputset)
# end in 5bit integer
x = 19
homomorphic_evaluation = circuit.simulate(x)
print(f"homomorphic_evaluation = {homomorphic_evaluation}")
Upon compiling and inspecting the MLIR (compiled circuit), we will observe the produced lookup desk.
module {
func.func @essential(%arg0: !FHE.eint<5>) -> !FHE.eint<1> {
%c21_i6 = arith.fixed 21 : i6
%cst = arith.fixed dense<[1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0]> : tensor<32xi64>
%0 = "FHE.apply_lookup_table"(%arg0, %cst) : (!FHE.eint<5>, tensor<32xi64>) -> !FHE.eint<1>
return %0 : !FHE.eint<1>
}
}
The strategy of evaluating two binary numbers by utilizing subtraction to find out which one is bigger could be effectively finished in FHE utilizing easy arithmetic. Binary comparability by subtraction leverages the properties of binary arithmetic. The core thought is that subtracting one quantity from one other reveals details about their relative sizes based mostly on the outcome and sure flags (just like the carry flag in processors) set through the operation.
In binary subtraction, if A is bigger than or equal to B, the result’s non-negative. If B is bigger, the result’s unfavorable, inflicting the carry flag to be 1.
That is means, if A>B, then carry=1, and 0 in any other case. Now we have to compute the carry bit kind proper to left and the final carry is the ultimate outcome. To hurry up FHE calculation we might compute 1+ A – B for every bit to make it constructive. This instance wants solely 2 bits to carry the residual. Then we left shift (<<) the carry bit by 2 positions and add the residual. The overall variety of all outcomes might be 8, which we will use along with the lookup desk to output the subsequent carry bit, like on this circuit.
# two numbers are have to introduced as bit arrays
# ---------------------------
# 0 0000 -> 1 much less (1+0-1), set the curry bit
# 1 0001 -> 0, equal (1+1-1) or (1+0-0)
# 2 0010 -> 0, higher (1+1-0)
# 3 0100 -> 0 (doesn't exists)
# carry bit set
# 5 1000 -> 1
# 6 1100 -> 1
# 7 1010 -> 1
# 8 1010 -> 1from concrete import fhe
desk = fhe.LookupTable([1,0,0,0,1,1,1,1])
# result's 1 if much less, 0 in any other case
@fhe.compiler({"x": "encrypted", "y": "encrypted"})
def fast_comparision(x, y):
carry = 0
# for all of the bits
for i in vary(4):
s = 1 + x[i] - y[i]
# left shift by 2 (carry << 4)
carry4 = carry*4 + s
carry = desk[carry4]
return curry
inputset = [([0,1, 1, 1], [1,0, 1,1])]
circuit = fast_comparision.compile(inputset)
homomorphic_evaluation = circuit.simulate([1,0,1, 0], [1,0,0,0])
print("homomorphic_evaluation =", homomorphic_evaluation)
This technique is way extra computationally costly than simply utilizing a lookup desk, like within the instance earlier than this one. Nonetheless, the reminiscence complexity is way much less right here, as a result of the lookup desk holds solely 8 values, leading to smaller analysis keys. And sure, as standard, nothing is ideal, as there’s a commerce off between reminiscence utilization vs CPU utilization and key sizes, relying on the tactic you choose.
Let’s have a look at the Bubble Kind, which is an easy comparison-based sorting algorithm that repeatedly steps by means of the listing to be sorted, compares every pair of adjoining gadgets, and swaps them if they’re within the mistaken order. The algorithm will get its identify as a result of smaller components “bubble” to the highest of the listing (starting of the array), whereas bigger components sink to the underside (finish of the array) with every iteration.
from concrete import fhe
import numpy as np@fhe.compiler({"in_array": "encrypted"})
def bubble_sort(in_array):
for i in vary(len(in_array)):
for j in vary(len(in_array)-1):
a = in_array[j]
b = in_array[j+1]
flag = a > b
# if a > b then swap the values
in_array[j] = flag * b + (1-flag) * a
in_array[j+1] = flag * a + (1-flag) * b
return in_array
inputset = [[3,0,0,0]]
circuit = bubble_sort.compile(inputset)
take a look at = [3,2,0,1]
test_clear = take a look at.copy()
test_fhe = take a look at.copy()
clear_evaluation = bubble_sort(test_clear)
#homomorphic_evaluation = circuit.encrypt_run_decrypt(test_fhe)
homomorphic_evaluation = circuit.simulate(test_fhe)
print(take a look at, "=> ", clear_evaluation, "=>", homomorphic_evaluation)
Bubble type is kind of gradual [O(n²)] however very reminiscence environment friendly [O(1)]. For a extra CPU environment friendly algorithm, you need to use Merge Kind. It really works on the precept of breaking down an inventory into smaller, extra manageable components (ideally right down to particular person components), sorting these components, after which merging them again collectively within the right order.
The merge type has a complexity of O(n log n) , making it one of the vital environment friendly sorting algorithms for big datasets. Nonetheless, the area complexity is O(n), because it requires extra area proportional to the array dimension for the non permanent merging course of.
Dynamic programming is a technique for fixing complicated issues by breaking them down into easier subproblems and fixing every of those subproblems simply as soon as, storing their options. The thought is that if you happen to can clear up the smaller subproblems effectively, you may then use these options to deal with the bigger drawback. Let’s take a Fibonacci numbers for instance.
The Fibonacci sequence is a sequence of numbers the place every quantity is the sum of the 2 previous ones, normally beginning with 0 and 1. The sequence usually goes 0, 1, 1, 2, 3, 5, 8, 13, and so forth. When fixing for the nth Fibonacci quantity utilizing dynamic programming, the strategy could be considerably extra environment friendly than the naive recursive strategy by avoiding redundant calculations.
As you may see, to unravel for F(6), we have to resolve two subproblems recursively: F(5) and F(4) and so forth. You possibly can word the options are overlapping, so the calculation of F(4) occurs each on the left and on the appropriate dimension of the tree. Clearly, we must always cache every distinctive outcome and thus compute it solely as soon as. Then our tree turns into quite simple. This strategy is known as memoization.
Nonetheless, within the context of Totally Homomorphic Encryption (FHE), memoization can’t usually be used because of the elementary traits and safety constraints of FHE. The explanation for that is that FHE permits operations to be carried out on encrypted information, that means the precise information values stay hid all through the computation.
The opposite strategy for dynamic programming is known as tabulation. Tabulation is a bottom-up strategy the place you clear up smaller subproblems first and use their options to construct options to greater issues. This technique is especially efficient for FHE as a consequence of its non recursive nature. Tabulation makes use of a desk the place on every step, you replace the present worth. On this instance we initialize a desk of 6 components with the bottom situations requiring the primary aspect to be 0 and the second aspect to be 1. The remainder of the weather are then initialized to zero: [0,1,0,0,0,0]. Then, we progress from left to proper.
This text marks the start of a sequence on Encrypted Knowledge Buildings and Algorithms. Up subsequent, I’ll delve into the usage of Graphs and Bushes, Machine Studying and AI throughout the realm of Totally Homomorphic Encryption (FHE). Subsequent installments will discover sensible purposes inside monetary trade.
—
Dive deeper into the world of encrypted information constructions and algorithms with the open supply IDE at FHE-Studio.com. Whether or not you’re trying to improve your tasks with top-tier safety protocols or just curious concerning the subsequent era of information privateness in software program improvement, FHE Studio is a free and open supply gateway to the FHE world. Develop, take a look at and share your circuits, and get suggestions from friends!
Searching for specialised experience? Our staff at FHE Studio might help you combine absolutely homomorphic encryption into your current tasks or develop new encrypted options tailor-made to your wants.
In the event you’ve discovered worth in our mission, contemplate supporting us. We’re dedicated to protecting FHE-Studio open and accessible, and each contribution helps us develop the mission.
- FHE-STUDIO.COM, an open supply FHE IDE
2. FHE Studio docs and sources, https://github.com/artifirm
3. Concrete FHE compiler: https://docs.zama.ai/concrete
4. Concrete ML is an open-source, privacy-preserving, machine studying framework based mostly on Totally Homomorphic Encryption (FHE). https://docs.zama.ai/concrete-ml
5. Microsoft SEAL, an open supply FHE library https://www.microsoft.com/en-us/analysis/mission/microsoft-seal/
6. HELib, a FHE library https://github.com/homenc/HElib
Except in any other case famous, all photographs are by the creator.