Amazon Q is a brand new generative synthetic intelligence (AI)-powered assistant designed for work that may be tailor-made to your small business. Amazon Q might help you get quick, related solutions to urgent questions, resolve issues, generate content material, and take actions utilizing the information and experience present in your organization’s data repositories and enterprise methods. Whenever you chat with Amazon Q, it gives fast, related data and recommendation to assist streamline duties, pace up decision-making, and spark creativity and innovation at work. For extra data, see Amazon Q Enterprise, now usually accessible, helps enhance workforce productiveness with generative AI.
This put up demonstrates the best way to construct a customized UI for Amazon Q Enterprise. The personalized UI permits you to implement particular options like dealing with suggestions, utilizing firm model colours and templates, and utilizing a customized login. It additionally allows conversing with Amazon Q via an interface customized to your use case.
Resolution overview
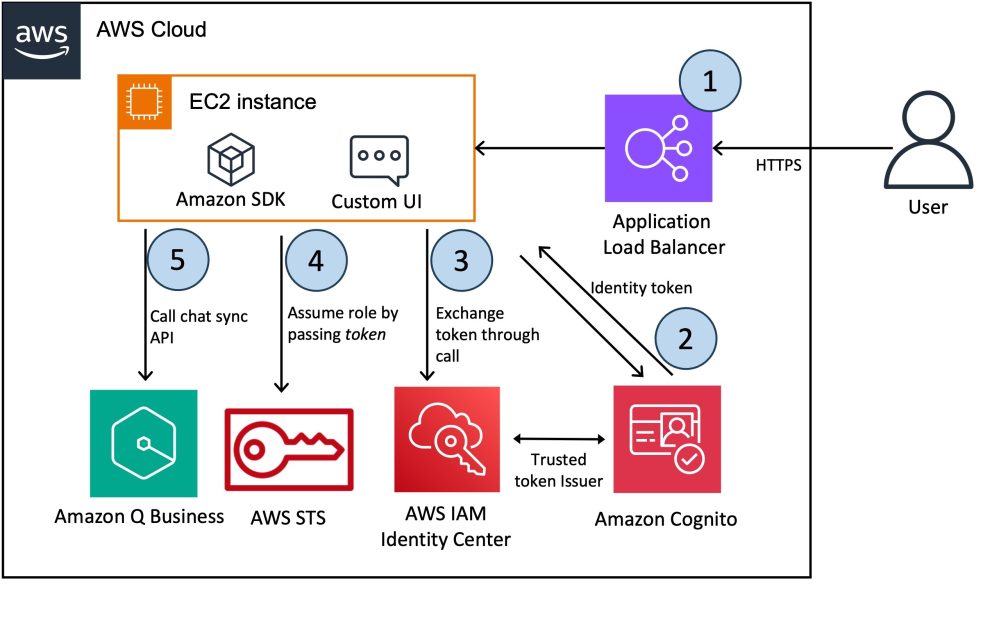
On this resolution, we deploy a customized net expertise for Amazon Q to ship fast, correct, and related solutions to your small business questions on prime of an enterprise information base. The next diagram illustrates the answer structure.
The workflow contains the next steps:
- The consumer accesses the chatbot software, which is hosted behind an Software Load Balancer.
- After the consumer logs in, they’re redirected to the Amazon Cognito login web page for authentication.
- This resolution makes use of an Amazon Cognito consumer pool as an OAuth-compatible identification supplier (IdP), which is required so as to alternate a token with AWS IAM Id Middle and afterward work together with the Amazon Q Enterprise APIs. For extra details about trusted token issuers and the way token exchanges are carried out, see Utilizing purposes with a trusted token issuer. If you have already got an OAuth-compatible IdP, you should use it as an alternative of setting an Amazon Cognito consumer pool.
- Provisioning native customers within the consumer pool and reconciling them with IAM Id Middle will be error-prone. You possibly can streamline the mixing of IAM Id Middle customers into the consumer pool by utilizing a federated IdP and making a second customized software (SAML) in IAM Id Middle. For directions, check with How do I combine IAM Id Middle with an Amazon Cognito consumer pool and the related demo video.
- The UI software, deployed on an Amazon Elastic Compute Cloud (Amazon EC2) occasion, authenticates the consumer with Amazon Cognito and obtains an authentication token. It then exchanges this Amazon Cognito identification token for an IAM Id Middle token that grants the appliance permissions to entry Amazon Q.
- The UI software assumes an AWS Id and Entry Administration (IAM) position and retrieves an AWS session token from the AWS Safety Token Service (AWS STS). This session token is augmented with the IAM Id Middle token, enabling the appliance to work together with Amazon Q. For extra details about the token alternate circulate between IAM Id Middle and the IdP, check with Find out how to develop a user-facing knowledge software with IAM Id Middle and S3 Entry Grants (Half 1) and Half 2.
- Amazon Q makes use of the chat_sync API to hold out the dialog.
- The request makes use of the next necessary parameters:
- applicationId – The identifier of the Amazon Q software linked to the Amazon Q dialog.
- userMessage – An end-user message in a dialog.
- Amazon Q returns the response as a JSON object (detailed within the Amazon Q documentation). The next are a couple of core attributes from the response payload:
- systemMessage – An AI-generated message in a dialog.
- sourceAttributions – The supply paperwork used to generate the dialog response. In Retrieval Augmentation Technology (RAG), this at all times refers to a number of paperwork from enterprise information bases which are listed in Amazon Q.
- The request makes use of the next necessary parameters:
Stipulations
For this walkthrough, it is best to have the next conditions:
- An AWS account arrange.
- A VPC the place you’ll deploy the answer.
- An IAM position within the account with enough permissions to create the required sources. When you’ve got administrator entry to the account, no further motion is required.
- An current, working Amazon Q software, built-in with IAM Id Middle. Should you haven’t set one up but, see Creating an Amazon Q software.
- Entry to IAM Id Middle to create a buyer managed software.
- An SSL certificates created and imported into AWS Certificates Supervisor (ACM). For extra particulars, check with Importing a certificates. Should you don’t have a public SSL certificates, comply with the steps within the subsequent part to generate a personal certificates.
Generate a personal certificates
If you have already got an SSL certificates, you’ll be able to skip this part.
You’ll obtain a warning out of your browser when accessing the UI in case you didn’t present a customized SSL certificates when launching the AWS CloudFormation stack. The directions on this part present you the best way to create a self-signed certificates. This isn’t really helpful for manufacturing use circumstances. You must acquire an SSL certificates that has been validated by a certificates authority, import it into ACM, and reference this when launching the CloudFormation stack. If you wish to proceed with the self-signed certificates (for improvement functions), it is best to be capable of proceed previous the browser warning web page. With Chrome, you will notice the message Your connection just isn’t non-public error message (NET::ERR_CERT_AUTHORITY_INVALID), however by selecting Superior, it is best to then see a hyperlink to proceed.
The next command generates a pattern self-signed certificates (for improvement functions) and uploads the certificates to ACM. You may as well discover the script on the GitHub repo.
Notice down the CertificateARN to make use of later whereas provisioning the CloudFormation template.
Provision sources with the CloudFormation template
The complete supply of the answer on within the GitHub repository and is deployed with AWS CloudFormation.
Select Launch Stack to launch a CloudFormation stack in your account and deploy the template:
This template creates separate IAM roles for the Software Load Balancer, Amazon Cognito, and the EC2 occasion. Moreover, it creates and configures these providers to run the end-to-end demonstration.
Present the next parameters for the stack:
- Stack title – The title of the CloudFormation stack (for instance,
AmazonQ-UI-Demo). - AuthName – A globally distinctive title to assign to the Amazon Cognito consumer pool. Ensure your area title doesn’t embody any reserved phrases, comparable to cognito, aws, or amazon.
- CertificateARN – The CertificateARN generated from the earlier step.
- IdcApplicationArn – That is the Amazon Useful resource Title (ARN) for the AWS Id Middle buyer software. Depart it clean on the primary run, as a result of that you must create the Amazon Cognito consumer pool as a part of this stack. This may create an IAM Id Middle software with an Amazon Cognito consumer pool because the trusted token issuer.
- LatestAMIId – The ID of the AMI to make use of for the EC2 occasion. We advise preserving the default worth.
- PublicSubnetIds – The ID of the general public subnet that can be utilized to deploy the EC2 occasion and the Software Load Balancer.
- QApplicationId – The present software ID of Amazon Q.
- VPCId – The ID of the present VPC that can be utilized to deploy the demo.

After the CloudFormation stack deploys efficiently, copy the next values on the stack’s Outputs tab:
- Viewers – Viewers to arrange the shopper software in IAM Id Middle
- RoleArn – ARN of the IAM position required to arrange the token alternate in IAM Id Middle
- TrustedIssuerUrl – Endpoint of the trusted issuer to arrange IAM Id Middle
- URL – The load balancer URL to entry the UI software
Create an IAM Id Middle software
The actions described on this part are one-time actions. The objective is to configure an software in IAM Id Middle to symbolize the appliance you’re constructing. Particularly, on this step, you configure IAM Id Middle to have the ability to belief the identification tokens by which your software will symbolize its authenticated customers. Full the next steps:
- On the IAM Id Middle console, add a brand new customized managed software.
- For Software sort, choose OAuth 2.0, then select Subsequent.

- Enter an software title and outline.
- Set Software visibility as Not seen, then select Subsequent.
- On the Trusted token issuers tab, select Create trusted token issuer.
- For Issuer URL, present the
TrustedIssuerUrlyou copied from the CloudFormation stack output. - Enter an issuer title and maintain the map attributes as E mail.
- Within the IAM Id Middle software authentication settings, choose the trusted token issuer created within the earlier step and add the Aud declare, offering the viewers you copied from the CloudFormation stack output, then select Subsequent.
- On the Specify software credentials tab, select Enter a number of IAM roles and supply the worth for RoleArn you copied from the CloudFormation stack output.
- Overview all of the steps and create the appliance.
- After the appliance is created, go to the appliance, select Assign customers and teams, and add the customers who could have entry to the UI software.
- On the Choose setup sort web page, select All purposes for service with similar entry, select Amazon Q from the Companies checklist, and select Belief purposes.
- After the IAM Id Middle software is created, copy the appliance ARN.
- On the AWS CloudFormation console, replace the stack and supply the IAM Id Middle software ARN for the parameter
IdcApplicationArn, then run the stack.
- When the replace course of is full, go to the CloudFormation stack’s Outputs tab and duplicate the URL offered there.
Customized UI
The CloudFormation stack deploys and begins the Streamlit software on an EC2 occasion on port 8080. To view the well being of the appliance working behind the Software Load Balancer, open the Amazon EC2 console and select Load Balancing beneath Goal teams within the navigation pane. For debugging functions, you may also connect with Amazon EC2 via Session Supervisor, a functionality of AWS Programs Supervisor.

To entry the customized UI, use the URL that you simply copied from the CloudFormation stack output. Select Join and use the identical electronic mail deal with for the customers that had been registered in IAM Id Middle.

After profitable authentication, you’re redirected to the customized UI. You possibly can improve it by implementing customized options like dealing with suggestions, utilizing your firms model colours and templates, and personalizing it to your particular use case.

Clear up
To keep away from future expenses in your account, delete the sources you created on this walkthrough. The EC2 occasion with the customized UI will incur expenses so long as the occasion is lively, so cease it if you’re carried out.
- On the CloudFormation console, within the navigation pane, select Stacks.
- Choose the stack you launched (
AmazonQ-UI-Demo), then select Delete.
Conclusion
On this put up, you realized the best way to combine a customized UI with Amazon Q Enterprise. Utilizing a customized UI tailor-made to your particular wants and necessities makes Amazon Q extra environment friendly and simple to make use of for your small business. You possibly can embody your organization branding and design, and have management and possession over the consumer expertise. For instance, you might introduce customized suggestions dealing with options.
The pattern customized UI for Amazon Q mentioned on this put up is offered as open supply—you should use it as a place to begin in your personal resolution, and assist enhance it by contributing bug fixes and new options utilizing GitHub pull requests. Discover the code, select Watch within the GitHub repo to obtain notifications about new releases, and verify again for the most recent updates. We welcome your ideas for enhancements and new options.
For extra data on Amazon Q enterprise, check with the Amazon Q Enterprise Developer Information.
Concerning the Authors
 Ennio Emanuele Pastore is a Senior Architect on the AWS GenAI Labs workforce. He’s an fanatic of all the pieces associated to new applied sciences which have a constructive impression on companies and normal livelihood. He helps organizations in reaching particular enterprise outcomes by utilizing knowledge and AI, and accelerating their AWS Cloud adoption journey.
Ennio Emanuele Pastore is a Senior Architect on the AWS GenAI Labs workforce. He’s an fanatic of all the pieces associated to new applied sciences which have a constructive impression on companies and normal livelihood. He helps organizations in reaching particular enterprise outcomes by utilizing knowledge and AI, and accelerating their AWS Cloud adoption journey.
 Deba is a Senior Architect on the AWS GenAI Labs workforce. He has intensive expertise throughout massive knowledge, knowledge science, and IoT, throughout consulting and industrials. He’s an advocate of cloud-centered knowledge and ML platforms and the worth they will drive for patrons throughout industries.
Deba is a Senior Architect on the AWS GenAI Labs workforce. He has intensive expertise throughout massive knowledge, knowledge science, and IoT, throughout consulting and industrials. He’s an advocate of cloud-centered knowledge and ML platforms and the worth they will drive for patrons throughout industries.
 Joseph de Clerck is a senior Cloud Infrastructure Architect at AWS. He leverages his experience to assist enterprises resolve their enterprise challenges by successfully using AWS providers. His broad understanding of cloud applied sciences allows him to plan tailor-made options on matters comparable to analytics, safety, infrastructure, and automation.
Joseph de Clerck is a senior Cloud Infrastructure Architect at AWS. He leverages his experience to assist enterprises resolve their enterprise challenges by successfully using AWS providers. His broad understanding of cloud applied sciences allows him to plan tailor-made options on matters comparable to analytics, safety, infrastructure, and automation.




/cdn.vox-cdn.com/uploads/chorus_asset/file/25588208/Megalopolis_Adam_Driver.png)



