With the Nationwide Institute of Requirements and Know-how (NIST) set to publish the primary Publish Quantum Cryptography (PQC) Requirements in a number of weeks, consideration is shifting to methods to put the brand new quantum-resistant algorithms into apply. Certainly, the variety of corporations with practices to assist others implement PQC is mushrooming and comprises acquainted (IBM, Deloitte, et al.) and unfamiliar names (QuSecure, SandboxAQ, and many others.).
The Migration to Publish-Quantum Cryptography venture, being run out of NIST’s Nationwide Cybersecurity Middle of Excellence (NCCoE), is operating at full-tilt and consists of on the order of 40 industrial contributors.
In its personal phrases, “The venture will interact trade in demonstrating use of automated discovery instruments to determine all cases of public-key algorithm use in an instance community infrastructure’s laptop and communications {hardware}, working techniques, software packages, communications protocols, key infrastructures, and entry management mechanisms. The algorithm employed and its goal could be recognized for every affected infrastructure element.”

Attending to that aim stays a WIP that began with NIST’s PQC program in 2016. NIST scientist Dustin Moody leads the PQC venture and talked with HPCwire about the necessity to take submit quantum cryptography significantly now, not later.
“America authorities is mandating their businesses to it, however trade in addition to going to should be doing this migration. The migration is just not going to be simple [and] it’s not going to be ache free,” stated Moody, whose Ph.D. specialised in elliptic curves, a generally used base for encryption. “Fairly often, you’re going to want to make use of subtle instruments which can be being developed to help with that. Additionally discuss to your distributors, your CIOs, your CEOs to ensure they’re conscious and that they’re planning for budgets to do that. Simply because a quantum laptop [able to decrypt] isn’t going to be constructed for, who is aware of, possibly 15 years, they could suppose I can simply put this off, however understanding that risk is coming before than you notice is necessary.”
Estimates differ wildly across the dimension of the risk however maybe 20 billion gadgets will should be up to date with PQC safeguarding. NIST has held 4 rounds of submissions and the primary set of requirements will embody algorithms chosen the primary three. These are the primary weapons in opposition to quantum decryption assault. The following spherical seeks to offer alternate options and, in some cases, considerably much less burdensome computational traits.
The dialogue with Moody was wide-ranging, if maybe slightly dry. He covers PQC technique and progress and the necessity to monitor the fixed circulate of latest quantum algorithms. Shor’s algorithm is the well-known risk however others are percolating. He notes that many submitted algorithms broke down below testing however says to not make a lot of that as that’s the character of the requirements growth course of. He talks about pursuing cryptoagility and presents a number of broad tips about preparation.
Moody additionally touched on geopolitcal rivalries amid what has been a typically collaborative worldwide effort.
“There are some exceptions like China by no means trusting america. They’re creating their very own PQC requirements. They’re truly very, similar to the algorithms [we’re using] however they have been chosen internally. Russia has been doing their very own factor, they don’t actually talk with the remainder of the world very a lot. I don’t have a number of info on what they’re doing. China, although they’re doing their very own requirements, did have researchers take part within the course of; they hosted one of many workshops within the discipline a number of years again. So the neighborhood is sufficiently small that persons are excellent at working collectively, even when typically the nation will develop their very own requirements,” stated Moody.
How quickly quantum computer systems will truly be capable to decrypt present RSA codes is way from clear, however early confidence that may be many many years has diminished. For those who’re searching for an excellent primer on the PQS risk, he really useful the Quantum Deal with Timeline Report launched in December by the World Danger Institute (GRI) as one (figures from its examine beneath).
HPCwire: Let’s discuss slightly bit concerning the risk. How massive is it and when do we have to fear
Dustin Moody: Effectively, cryptographers have identified for a number of many years that if we’re in a position to construct a large enough quantum laptop, it can threaten all the public key crypto techniques that which we use right this moment. So it’s a it’s a severe risk. We don’t know when a quantum laptop could be constructed that’s massive sufficient to assault present ranges of safety. There’s been estimates of 10 to fifteen years, however you already know, no person is aware of for sure. We have now seen progress in corporations constructing quantum computer systems — techniques from IBM and Google, for instance, are getting bigger and bigger. So that is undoubtedly a risk to take significantly, particularly as a result of you possibly can’t simply wait till the quantum laptop is constructed after which say now we’ll fear about the issue. We have to resolve this 10 to fifteen years prematurely to guard your info for a very long time. There’s a risk of harvest-now-decrypt-later that helps you perceive that.
HPCwire: Marco Pistoia, who leads quantum analysis for JPMorgan Chase, stated he’d seen a examine suggesting as few as 1300 or so logical qubits may be capable to break typical RSA code, though it could take six months to take action. That was a yr in the past. It does seem to be our capability to execute Shor’s algorithm on these techniques is bettering, not simply the brute power, however our cleverness in getting the algorithm to run.
Dustin Moody: Yep, that’s true. And it’ll take a number of logical qubits. So we’re not there but. However yeah, progress has been made. It’s important to resolve the issue solved and migrate to new options earlier than we ever get to that time,
HPCwire: We are inclined to give attention to Shor’s algorithm as a result of it’s a direct risk to the present encryption strategies. Are there others within the wings that we must be apprehensive about?
Dustin Moody: There’s numerous quantum algorithms that we’re conscious of, Shor being one in every of them, Grover’s being one other one which has an affect on cryptography. However there’s loads of different quantum algorithms that do attention-grabbing issues. So every time anybody is designing the crypto system, they’ve to try all these and see in the event that they appear like they might assault the system in any method? There’s sort of a listing of I don’t know, possibly round 15 or in order that doubtlessly folks must sort of have a look at him and work out, do I would like to fret about these.
HPCwire: Does NIST have that record someplace?
Dustin Moody: There was a man at NIST who stored up such a listing. I believe he’s at Microsoft, now. It’s been a short time, however he maintained one thing known as the Quantum Algorithms Zoo.
HPCwire: Let’s get again to the NIST effort to develop quantum-resistant algorithms. As I perceive it, the method started being round 2016 has gone via this iterative course of the place you invite submissions of potential quantum resistant algorithms from the neighborhood, then take a look at them and provide you with some picks; there have been three rounds accomplished and within the strategy of turning into requirements, with an ongoing fourth spherical. Stroll me via the venture and progress.
Dustin Moody: So these sorts of cryptographic competitions have been performed up to now to pick among the algorithms that we use right this moment. [So far] a extensively used block cypher was chosen via a contest. Extra just lately a hash operate. Again in 2016, we determined to do one in every of these [competitions] for brand new submit quantum algorithms that we would have liked requirements for. We let the neighborhood find out about that. They’re all excited and we received 82 submissions of which 69 met sort of the necessities that we’d got down to be concerned. Then we had a course of that over six or seven years [during which] we evaluated them going via a interval of rounds. In every spherical, we went additional right down to probably the most promising to advance the tons of labor happening in there, each internally at NIST, and by the cryptographic neighborhood, doing analysis and benchmarks and experiments and all the pieces.
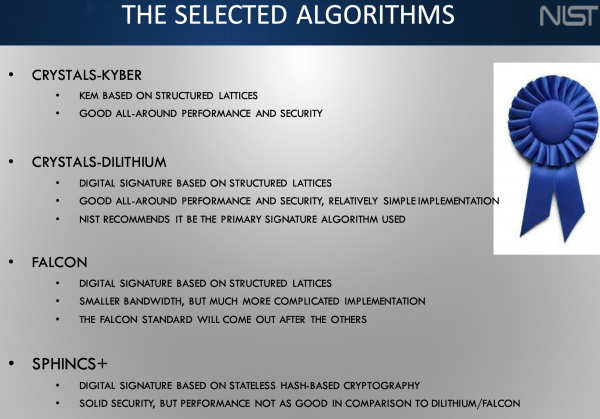
The third spherical had seven finalists and eight alternate concluded in July of 2022, the place we introduced objects that we’d be standardizing because of this, that included one encryption algorithm and three signature algorithms. We did additionally maintain a number of encryption algorithms on right into a fourth spherical for additional examine. They weren’t fairly able to be chosen for standardization. That fourth spherical remains to be ongoing and can in all probability finish as this fall, and we’ll decide one or two of these to additionally standardize. We’ll have two or three encryption [methods] and three signatures as nicely.
HPCwire: It seems like a comparatively easy course of?
Dustin Moody: That course of received a number of consideration from the neighborhood. A number of the algorithms ended up being damaged, some late within the course of — that’s sort of the character of how this factor works. That’s the place we at the moment are. We’re nearly performed writing the requirements for the primary ones that we chosen, our anticipated date is publishing them this summer season. The fourth spherical will finish this fall, after which we’ll write requirements for these that can take one other yr or two.
We even have ongoing work to pick a number of extra digital signature algorithms as nicely. The rationale for that’s so most of the algorithms we chosen are primarily based on what are known as lattices; they’re probably the most promising household, [with] good efficiency, good safety. And for signatures, we had two primarily based on lattices, after which one not primarily based on lattices. The one which wasn’t primarily based on lattices — it’s known as SPHINCS+ — seems to be greater and slower. So if purposes wanted to make use of it, it won’t be ideally suited for them. We needed to have a backup not primarily based on lattices that might get used simply. That’s what this ongoing digital signature course of is about [and] we’re encouraging researchers to try to design new options that aren’t primarily based on lattices which can be higher performing.
HPCwire: When NIST assesses these algorithms, it should look to see what number of computational assets are required to run them?
Dustin Moody: There’s particular analysis standards that we have a look at. Primary is safety. Quantity two is efficiency. And quantity three is that this laundry record of all the pieces else. However we work internally at NIST, we’ve a workforce of specialists and attempt to work with cryptography and trade specialists around the globe who’re independently doing it. However typically we’re doing joint analysis with them within the discipline.
Safety has a large variety of methods to have a look at it. There’s the theoretical safety, the place you’re attempting to create safety proofs the place you’re attempting to say, ‘in case you can break my crypto system, then you possibly can break this difficult mathematical downside.’ And we may give a proof for that and since that onerous mathematical downside has been studied, that provides us slightly bit extra confidence. Then it will get sophisticated as a result of we’re used to doing this with classical computer systems and taking a look at how they will assault issues. However now we’ve to have a look at how can quantum computer systems assault issues and so they don’t but exist. We don’t know their efficiency. capabilities. So we’ve to extrapolate and do one of the best that we are able to. However it’s all thrown into the combo.
Usually, you don’t find yourself needing supercomputers. You’re in a position to analyze how lengthy would the assaults take, what number of assets they take, in case you have been to totally tried to interrupt the safety parameters at present ranges. The parameters are chosen in order that it’s [practically] infeasible to take action. You may work out, if I have been to interrupt this, it could take, you already know, 100 years, so there’s no use in truly attempting to do this until you sort of discover a breakthrough to discover a completely different method. (See descriptive record of NIST strengths classes at finish of article)
HPCwire: Do you take a look at on right this moment’s NISQ (near-term intermediate scale quantum) computer systems?
Dustin Moody: They’re too small proper now to essentially have any affect in taking a look at how will a bigger quantum laptop fare in opposition to concrete parameters chosen at excessive sufficient safety ranges. So it’s extra theoretical, while you’re determining how a lot assets it could take.
HPCwire: So summarizing slightly bit, you suppose within the fall you’ll end this final fourth spherical. These would all be candidates for requirements, which then anybody may use for incorporation into encryption schemes that may be quantum laptop resistant.
Dustin Moody: That’s right. The principle ones that we anticipate to make use of have been already chosen in our first batch. So these are sort of the first ones, most individuals will use these. However we have to have some backups in case you already know, somebody comes up with a brand new breakthrough.
HPCwire: When you choose them do you intentionally have a spread by way of computational necessities, figuring out that not everybody goes to have supercomputers at their doorstep. Many organizations may have to make use of extra modest assets when operating these encryption codes. So folks may decide and select slightly bit primarily based on the computational necessities.
Dustin Moody: Sure, there’s a spread of safety classes from one to 5. Class 5 has the best safety, however efficiency is impacted. So there’s a commerce off. We embrace parameters for classes one, three, a 5 so folks can select the one which’s greatest suited to their wants.
 HPCwire: Are you able to discuss slightly bit concerning the Migration to PQC venture, which can be I imagine in NIST initiative to develop a wide range of instruments for implementingPQC What’s your involvement? How is that going?
HPCwire: Are you able to discuss slightly bit concerning the Migration to PQC venture, which can be I imagine in NIST initiative to develop a wide range of instruments for implementingPQC What’s your involvement? How is that going?
Dustin Moody: That venture is being run by NIST’s Nationwide Cybersecurity Middle of Excellence (NCCoE). I’m not one of many managers however I attend all of the conferences and I’m there to help what goes on. They’ve collaborated with…I believe the record is up 40 or 50 trade companions and the record is on their web site. It’s a extremely robust collaboration. A number of these corporations on their very own would usually be competing with every however right here, they’re all working for the widespread good of constructing the migration as easy as potential, getting expertise creating instruments that persons are going to want to do cryptographic inventories. That’s sort of one of many first steps that a corporation goes to want to do. Making an attempt to ensure all the pieces will probably be interoperable. What classes can we study as we. Some persons are additional alongside than others and the way can we share that info greatest? It’s actually good to have weekly calls, [and] we maintain occasions every so often. Principally these trade collaborators are driving it and speaking with one another and we simply sort of manage them collectively and assist them to maintain shifting.
HPCwire: Is there any effort to construct greatest practices on this space? One thing that that NIST and these collaborators from trade and academia and DOE and DOD may all present? It might be maybe have the NIST stamp of authority on greatest practices for implementing quantum resistant cryptography.
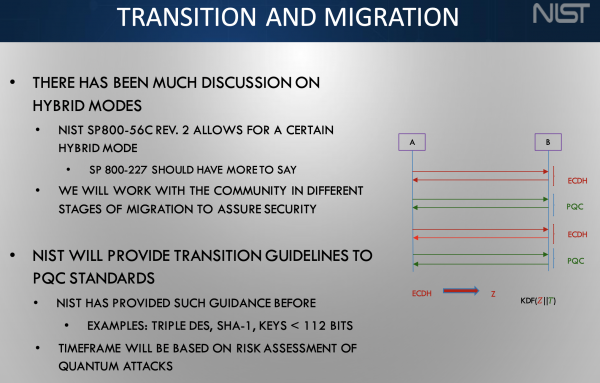
Dustin Moody: Effectively, the requirements that my workforce is writing, and people are written by NIST and people are the algorithms that folks will implement. Then they’ll additionally then get examined and validated by a few of our labs at NIST. The migration venture is producing paperwork, in a sequence (NIST SP 1800-38A, NIST SP 1800-38B, NIST SP 1800-38C) and people are up to date every so often, the place they’re sharing what they’ve realized and placing greatest apply on this. They’re NIST paperwork, written collectively with the NIST workforce and with these collaborators to share what they’ve received up to now.
HPCwire: What can the potential consumer neighborhood do to be concerned? I notice the venture is kind of mature, it’s been round for some time, and also you’ve received tons of people that who’ve been concerned already. Are we on the stage the place the primary contributors are working with one another and NIST in creating these algorithms, and it’s now a matter of kind of monitoring the instruments that come out.
Dustin Moody: I might say each group must be turning into educated on understanding the quantum risk, figuring out what’s happening with standardization, figuring out that you just’re going to want emigrate, and what that’s going to contain your group. It’s not going to be simple and ache free. So planning forward, and all that. In the event that they need to be a part of that that collaboration (Migration to PQC), persons are nonetheless becoming a member of every so often and it’s nonetheless open if they’ve one thing that they’ve received to share. However for many organizations or teams, it’s going to be simply attempting to create your plan getting ready for the migration. We would like you to attend until the ultimate requirements are revealed, so that you’re not implementing the one thing that’s 99% the ultimate normal, we would like you to attend till that’s there, however you possibly can put together now.
HPCwire: When will they be closing?
Dustin Moody: Of the 4 that we chosen, three of them. We put out draft requirements a yr in the past, received public suggestions, and have been revising since. The ultimate variations are going to be revealed this summer season. We don’t have an actual date, however it can, it’ll be this summer season.
HPCwire: At that time, will a wide range of necessities will come round utilizing these algorithms, for instance within the U.S. authorities and maybe in trade requiring compliance?
Dustin Moody: Technically NIST isn’t a regulatory company. So sure, US authorities can. I believe the OMB says that every one businesses want to make use of our requirements. So the federal authorities has to make use of the requirements that we use for cryptography, however we all know {that a} wider viewers trade in america and globally tends to make use of the algorithms that we standardized as nicely.
HPCwire: We’re in a world during which geopolitical tensions are actual. Are we apprehensive about rivals from China or Russia, or different competing nations not sharing their advances? Or is the cryptoanalyst neighborhood sufficiently small that these sorts of issues aren’t more likely to occur as a result of the folks know one another?
 Dustin Moody: There’s a actual geopolitical risk by way of who will get the quantum laptop quickest. If China develops that and so they’re in a position to break into our cryptography, that’s a that’s an actual risk. By way of designing the algorithms and making the requirements, it’s been a really cooperative effort internationally. Business advantages when lots of people are utilizing the identical algorithms all around the world. And we’ve seen different international locations in world requirements organizations say they’re going to make use of the algorithms that have been concerned in our course of.
Dustin Moody: There’s a actual geopolitical risk by way of who will get the quantum laptop quickest. If China develops that and so they’re in a position to break into our cryptography, that’s a that’s an actual risk. By way of designing the algorithms and making the requirements, it’s been a really cooperative effort internationally. Business advantages when lots of people are utilizing the identical algorithms all around the world. And we’ve seen different international locations in world requirements organizations say they’re going to make use of the algorithms that have been concerned in our course of.
There are some exceptions like China by no means trusting america. They’re creating their very own PQC requirements. They’re truly very, similar to the algorithms [we’re using] however they have been chosen internally. Russia has been doing their very own factor, they don’t actually talk with the remainder of the world very a lot. I don’t have a number of info on what they’re doing. China, although they’re doing their very own requirements, did have researchers take part within the course of; they hosted one of many workshops within the discipline a number of years again. So the neighborhood is sufficiently small that persons are excellent at working collectively, even when typically the nation will develop their very own requirements.
HPCwire: How did you become involved in cryptography? What drew you into this discipline?
Dustin Moody: Effectively, I like math and the mathematics I used to be finding out has some purposes in cryptography, particularly, one thing known as elliptic curves, and there’s crypto techniques we use right this moment which can be primarily based on the curve, which is that this stunning mathematical object that in all probability nobody ever thought they might be of any use within the in the true world. However it seems they’re for cryptography. In order that’s sort of my hook into cryptography.
I ended up at NIST as a result of NIST has elliptic curve cryptography requirements. I didn’t know something about submit quantum cryptography. Round 2014, my boss stated, we’re going to place you on this venture coping with submit quantum cryptography and I used to be like, ‘What’s this? I’ve no thought what that is.’ Inside a few years, it sort of actually took off and grew and has change into this excessive precedence for america authorities. It’s been a sort of a enjoyable journey to be on.
HPCwire: Win poor health the PQC venture simply proceed or will it wrap up in some unspecified time in the future?
Dustin Moody: We’ll proceed for various years. We nonetheless have the fourth spherical to complete. We’re nonetheless doing this extra digital signature course of, which can take a number of extra years. However then once more, each all the pieces we do sooner or later wants to guard in opposition to quantum computer systems. So these preliminary requirements will get revealed, they’ll be performed in some unspecified time in the future, however all future cryptography requirements must take the quantum risk under consideration. So it’s sort of in-built that we’ve to maintain going for the longer term.
HPCwire: When you discuss to the seller neighborhood, all of them say, “Encryption has been applied in such a haphazard method throughout techniques that it’s in all places, and that in merely discovering the place it exists in all these issues is tough.” The true aim, they argue, must be to maneuver to a extra modular predictable method. Is there a method NIST can affect that? Or the choice of the algorithms can affect that?
Dustin Moody: Yes, and no. It’s very difficult. That concept you’re speaking about, typically the phrase cryptoagility will get thrown on the market in that route. Lots of people are speaking about, okay, we’re going to want emigrate these algorithms, this is a chance to revamp techniques and protocols, possibly we are able to do it slightly bit extra intelligently than we did up to now. On the identical time, it’s tough to do this, since you’ve received so many interconnected items doing so many issues. So it’s difficult to do, however we’re encouraging folks and having numerous conversations like with the migration and PQC venture. We’re encouraging folks to consider this, to revamp techniques and protocols while you’re designing your purposes. Understanding I have to transition to those algorithms, possibly I can redesign my system in order that if I have to improve once more, in some unspecified time in the future, it’ll be a lot simpler to do. I can maintain observe of the place my cryptography is, what occurs after I’m utilizing it, what info and defending. I hope that we’ll get some profit out of this migration, however it’s, it’s actually going to be very tough, sophisticated and painful as nicely.
HPCwire: Do you might have an off the highest of your head guidelines kind of 5 issues you have to be serious about now to organize for submit quantum cryptography?
Dustin Moody: I’d say primary, simply know that the migration is coming. America authorities is mandating their businesses to it, however trade in addition to going to should be doing this migration. The migration is just not going to be simple, it’s not going to be ache free. Try to be educating your self as to what PQC is, the entire quantum risk, and beginning to determine, the place are you utilizing cryptography, what info is protected with cryptography. As you famous, that’s not as simple accurately. “Fairly often, you’re going to want to make use of subtle instruments which can be being developed to help with that. Additionally discuss to your distributors, your CIOs, your CEOs to ensure they’re conscious and that they’re planning for budgets to do that. Simply because a quantum laptop [able to decrypt] isn’t going to be constructed for, who is aware of, possibly 15 years, they could suppose I can simply put this off, however understanding that risk is coming before than you notice is necessary.”
HPCwire: Thanks on your time!
In accordance with the second and third objectives above (Submission Necessities and Analysis Standards for the Publish-Quantum Cryptography Standardization Course of), NIST will base its classification on the vary of safety strengths supplied by the prevailing NIST requirements in symmetric cryptography, which NIST expects to supply vital resistance to quantum cryptanalysis. Particularly, NIST will outline a separate class for every of the next safety necessities (listed so as of accelerating strength2 ):
1) Any assault that breaks the related safety definition should require computational assets akin to or higher than these required for key search on a block cipher with a 128-bit key (e.g. AES-128)
2) Any assault that breaks the related safety definition should require computational assets akin to or higher than these required for collision search on a 256-bit hash operate (e.g. SHA-256/ SHA3-256)
3) Any assault that breaks the related safety definition should require computational assets akin to or higher than these required for key search on a block cipher with a 192-bit key (e.g. AES-192)
4) Any assault that breaks the related safety definition should require computational assets akin to or higher than these required for collision search on a 384-bit hash operate (e.g. SHA-384/ SHA3-384)
5) Any assault that breaks the related safety definition should require computational assets akin to or higher than these required for key search on a block cipher with a 256-bit key (e.g. AES-256)
Associated









/cdn.vox-cdn.com/uploads/chorus_asset/file/25547838/YAKZA_3840_2160_A_Elogo.jpg)
